My OpenCanary in the Cloud was not logging SMB requests properly and I finally made time to look and understand the problem. Naturally, I wanted to test the share and look at the logs when I did it – so I opened a browser and……there were some files that I had not put there….!!!
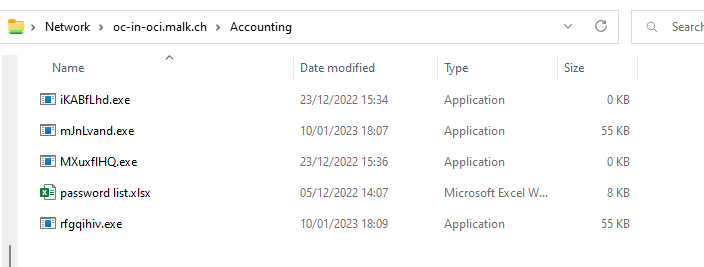
It seems some miscreant found the SMB share and decided to host some malware from it. This was not what I expected when I left the share open to write to – but I would and should have spotted it had the logging been working.
It seems someone uploaded (or attempted to, at least) two malware files on 23rd December. I can only assume their antivirus kicked in and stopped the copy, leaving the zero-sized files in place.
This year, on 10th January, possibly the same person – now with antivirus disabled – managed to upload two files to the share. My Defender was not impressed with the files as you can see.
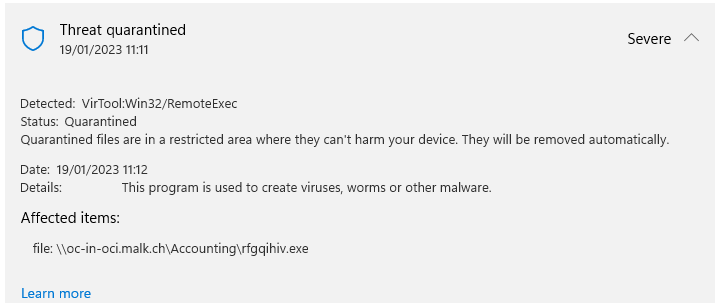
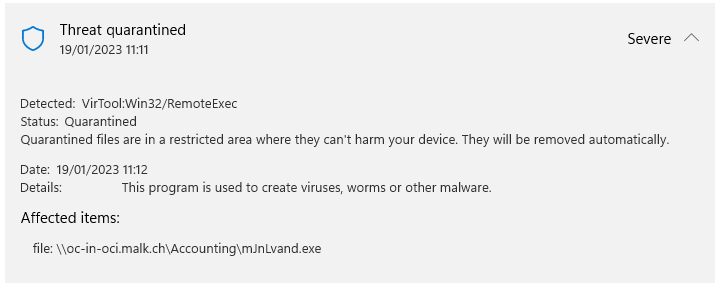
As I don’t want to be involved in some malware campaign, serving files to victims around the Internet, I let it quarantine and delete them and set a cronjob to move the files into an isolated folder every half an hour. I would have uploaded these files to VirusTotal but they were clearly known to AV vendors.
It’s a lesson to me that I allowed these files to be hosted for a week before finding them and deleting them; I replaced them with some Canary Tokens and will report on what clicks, if any, they get.
The OpenCanary in Oracle Cloud guide has been updated too, adding the configuration change for SMB logging, log rotation, crontab entry to stop what might be a memory leak in OpenCanary and more. I recommend you have a play with a free host!


